Healthcare Identity: Band-Aid Treatment vs Real Identity Defense
Traditional IAM was designed to:
- Pass audits
- Check regulatory boxes
- Document access
The result in healthcare environments:
- Stolen clinician credentials still work
- EHR sessions are reused and shared
- “Authorized access” misuse goes undetected
Identity Pain Areas For Healthcare CISOs & CIOs
Passwords as a Band-Aid for Patient Data
Passwords and OTPs mask access risk while enabling breaches of EHRs and clinical systems.
Privileged Access with No Immunity
Admins, clinicians, and vendors access crown-jewel systems using static secrets.

MFA That Treats Security, Not Care
Push-based MFA adds friction in time-critical clinical workflows without stopping attackers.
Compliance That Looks Healthy on Paper
Audits pass, but identity-driven misuse continues in live care environments.
How Rainbow Secure Treats the Root Cause
This is how healthcare organizations reduce identity risk without slowing patient care.
Cognitive Passwordless Access
Replaces passwords and OTPs with color, format, and style-based human verification.
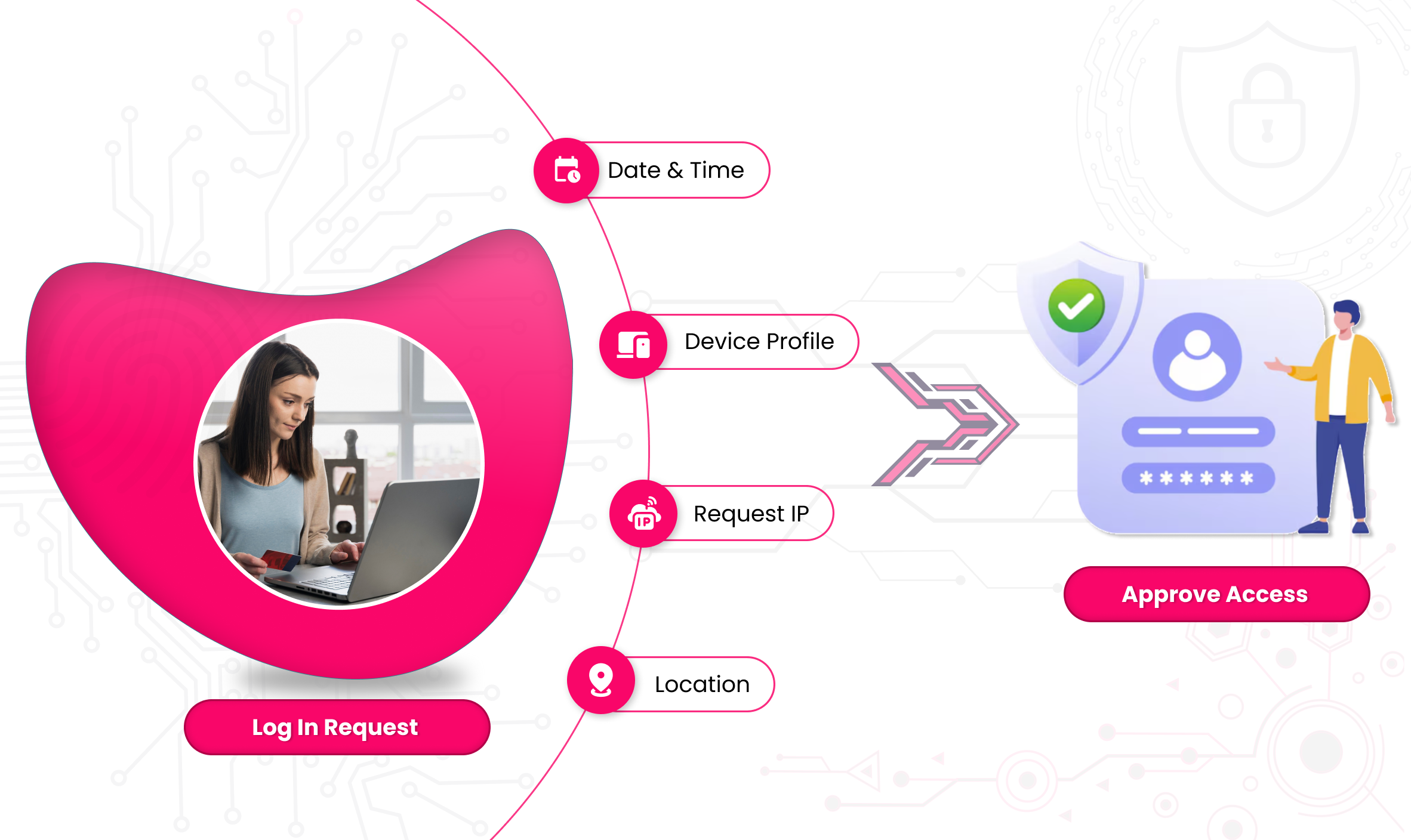
MFA Without Clinical Side Effects
Authentication validates real human intent — not blind approvals.
Privilege Without Chronic Exposure
Elevated and shared access without reusable credentials or standing secrets.
Defensible Identity Assurance
Continuous, human-verified access with audit-ready evidence.

Rainbow Cognitive Identity Defense — Core Capabilities
-
Cognitive MFA
Human-bound authentication using color, style, and pattern recognition tto stop phishing, replay, and MFA-fatigue attacks.
-
Unified SSO
Seamless access across EHRs, clinical apps, SaaS, and legacy systems — without increasing credential exposure.
-
Privileged & Shared Access
Secure clinical, IT, and vendor access without static or reusable secrets.
-
User Lifecycle Management
Automated joiner-mover-leaver enforcement aligned to clinical roles and duties.
-
Risk Monitoring & Compliance
Continuous identity-risk visibility with evidence-rich reporting aligned to healthcare regulations.


Why Healthcare Is Especially Exposed
Healthcare environments uniquely combine:
- Life-critical clinical workflows
- Third-party vendors and medical device access
- Zero tolerance for downtime or access delays
- Highly privileged users (doctors, nurses, technicians)
- Remote and emergency access requirements
Cognitive Identity Defence proves the person behind access.
Where Healthcare Teams Use Rainbow Secure
EHR & Patient Record Systems
Protect patient data without interrupting care delivery.
Clinical & Diagnostic Platforms
Secure frequent clinician access without password reuse.
Remote & On-Call Access
Enable secure access during emergencies without added friction.
Medical Device & Vendor Access
Continuous, human-verified access with audit-ready evidence.
Custom Healthcare Applications — Where Band-Aids Fall Off
Healthcare organizations rely heavily on:
-
Custom EHR extensions
-
Lab and radiology systems
-
Telemedicine platforms
-
Medical device management applications
- Traditional IAM requires custom integrations and partial coverage — leaving critical systems exposed.
- Rainbow Secure applies Cognitive Identity Defense uniformly across custom and legacy healthcare applications, closing gaps that band-aid controls cannot.

What Healthcare Leaders Actually Need
- Assume credentials will fail
- Do not rely on clinician vigilance
- Work during emergencies
- Reduce breach response and audit fatigue
Healthcare Compliance Frameworks Supported
- ISO 27001 (Healthcare Implementations)
- NIST Cybersecurity Framework (CSF)
- HIPAA
- HITECH Act
- HITRUST CSF
Ready To Get Started ? We're Here To Help
Start your journey with us today. It’s quick, easy, and we’re here to help you every step of the way.
Let’s Talk





















