Cognitive Identity Defense for the Era of AI & Identity Warfare
- Creative for humans.
- Cognitively disruptive for attackers.
- Hostile to bots and AI-driven identity attacks.
Rainbow Secure is not another IAM platform.
It is a Cognitive Identity Attack Defense Mechanism — built to defend identities the way modern attackers actually operate: through psychology, automation, deception, and scale.
Traditional identity systems assume users behave perfectly
Modern attackers know better.Rainbow Secure is built on a simple truth
- Passwords will leak
- Humans will be tricked
- MFA will be abused

Introducing Rainbow Secure Technology
Rainbow Secure Technology redefines digital security by creating authentication experiences that humans recognize instantly—but bots cannot mimic. It combines behavioral insights, contextual awareness, and advanced verification to keep your systems safe without slowing users down.
Our solution adapts in real time, analyzing risk, environment, and user behavior to provide multi-factor authentication that’s intelligent and invisible. This ensures only legitimate users gain access, reducing breaches and credential abuse effortlessly.
See it in action: the Rainbow Secure Technology Intro Video demonstrates how our system blends security with usability, delivering protection that’s seamless for users but alien to attackers. Explore the future of authentication today.
What Makes Rainbow Secure Different
Rainbow Secure puts identity security at the center, delivering advanced threat detection, rapid response, and audit‑ready compliance alongside
modern identity management.

Rainbow Secure focuses on defending identity under active attack.
Security that users remember. Confusion that attackers cannot automate.
-
Creative & Cognitive MFA
Rainbow Secure blends Cognition, Context, and Cryptography to make attacks fail and users succeed — using intuitive security layers of colors, fonts, and formatting patterns.
-
AI Powered Risk Reduction
Disrupts brute force, credential stuffing, and malware-driven identity attacks before they happen.
-
Adaptive Identity Defense
Applies real-time cognitive checks across location, device, time, and login behavior, allowing only genuine users to pass through.

Safe, Intuitive , and Frictionless Identity Access
Stronger identity defense, lower operational friction, and flexible design—giving SMBs and enterprises resilient identity security within budget.
Enterprise-Grade Identity Control & Compliance
Role-based access control to govern permissions, support compliance readiness, and enable intelligence-driven identity risk monitoring and alerts.
Unified User & Identity Operations
A centralized console to manage users, groups, and identity policies with real-time alerts, access visibility, and session-level oversight.
End-to-End Identity Security & Encryption
AES-256 encryption protects authentication artifacts and identity data, while cognitive MFA and SSO deliver secure, seamless access.
Introducing Rainbow Secure Technology
Our advanced authentication blocks major cyber threats including phishing, password reuse, keylogging, brute-force, and AI-driven attacks.
By adding a multi-dimensional, color- and style-based MFA layer, it makes stolen credentials useless while delivering
a seamless and secure login experience built for today’s evolving threats.
How Rainbow Secure Works
Security That Aligns with User Behavior — While Disrupting Adversaries.
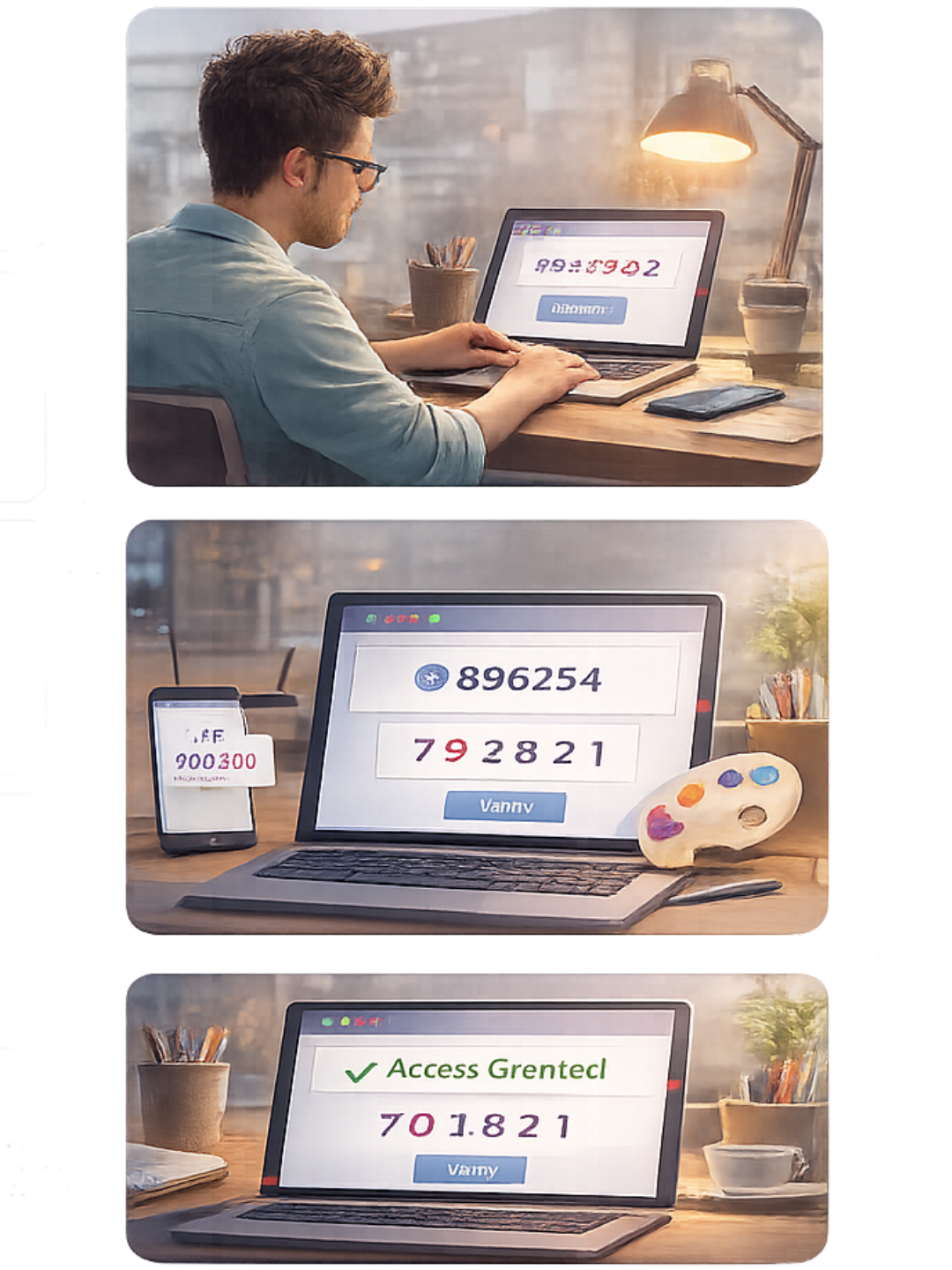

A Simple Three-Step Approach
Design Your Cognitive Login
Create authentication experiences with color, fonts and size which humans recognize and bots cannot mimic.
Authenticate with Context & Cognition
Multi-factor authentication that adapts to behavior, risk, and environment.
Secure Access to Every Application
Unify access across 1,000+ cloud and custom applications with powerful SSO — reinforced by advanced identity defense. One login. Zero compromise
How Identity Defense Differs From Traditional IAM
Compare what modern identity threats demand — and what today’s solutions actually deliver.
| Capability / Category | Player 1 | Player 2 | Player 3 | Rainbow Secure |
|---|---|---|---|---|
| Category Focus | Identity Management | IAM + MFA | Passwordless & IAM | Cognitive Identity Defense |
| Cognitive Authentication | ❌ | ❌ | ⚠️ | ✅ |
| Phishing & Fake Login Disruption | ❌ | ❌ | ⚠️ | ✅ (Strong) |
| Defense Against MFA Fatigue & Abuse | ❌ | ⚠️ | ⚠️ | ✅ (Native) |
| Bot & Automated Attack Resistance | ⚠️ | ⚠️ | ⚠️ | ✅ (Purpose-Built) |
| Real-Time Cognitive Risk Detection | ⚠️ | ⚠️ | ⚠️ | ✅ (AI-Driven) |
| Contextual Identity Defense (Device, Location, Behavior) | ⚠️ | ⚠️ | ⚠️ | ✅ (Adaptive) |
| Identity Threat Detection (ITDR) | ⚠️ | ⚠️ | ⚠️ | ✅ (Login-centric) |
| SSO | ✅ | ✅ | ✅ | ✅ |
| MFA / Passwordless Options | ✅ | ✅ | ✅ | Cognitive & Contextual |
| User Lifecycle Mgmt | ✅ | ⚠️ | ⚠️ | ✅ |
| Privileged & Shared Access | ⚠️ | ⚠️ | ⚠️ | ✅ (Integrated) |
| Risk Monitoring & Compliance | ⚠️ | ⚠️ | ⚠️ | ✅ (Continuous) |
| Role-Based Access Control | ✅ | ✅ | ⚠️ | ✅ |
| Adaptive Security Policies | ⚠️ | ⚠️ | ⚠️ | ✅ (Real-Time) |
| Attack Economics Reduction | ❌ | ❌ | ❌ | ✅ (Core Strategy) |
| Phishing Kit + Automation Blocking | ❌ | ❌ | ❌ | ✅ |
| AI-Driven Adversary Modeling | ❌ | ❌ | ❌ | ✅ |
| Designed for Human Cognition | ❌ | ❌ | ❌ | ✅ |
| Ease of Legitimate User Access | ⚠️ | ⚠️ | ⚠️ | Smooth & Intuitive |
Identity Defense Delivered Through Familiar Capabilities

-
MFA
Cognitive, contextual, and non-replicable authentication.
-
User Lifecycle Management
Identity control from onboarding to exit — without gaps.
-
Single Sign On
Secure access to applications without weakening identity defense.
-
Privileged and Shared Access
Protect high-risk access paths from misuse and abuse.
-
Risk Monitoring and Compliance
Continuous risk visibility with audit-ready insights.







