24/7 Risk Analytics & AI-Driven Login Monitoring
Security That Watches Every Login — Without Ever Blinking.
- Login attempts never stop.
- Attackers never pause.
Rainbow Secure continuously monitors authentication activity across your entire environment using advanced risk analytics and intelligent behavioral modeling to detect abnormal login patterns in real time.
- Every login is evaluated.
- Every session is analyzed.
- Every deviation is surfaced.



Why It Matters
Identity-driven attacks are now the primary cause of modern breaches.
Attackers rely on
- Credential stuffing.
- Password spraying
- Phishing-harvested credentials
- MFA fatigue exploitation
- Bot-driven automation
They do not analyze
- Behavioral deviations.
- Login velocity spikes
- Geographic inconsistencies
- MFA fatigue exploitation
- Device anomalies
Without continuous monitoring
- Compromised accounts remain active
- Suspicious activity blends into normal traffic
- High-risk sessions go unchallenged
- Privilege escalation unnoticed
- Repeated attack patterns remain undetected
- Security gaps persist without remediation
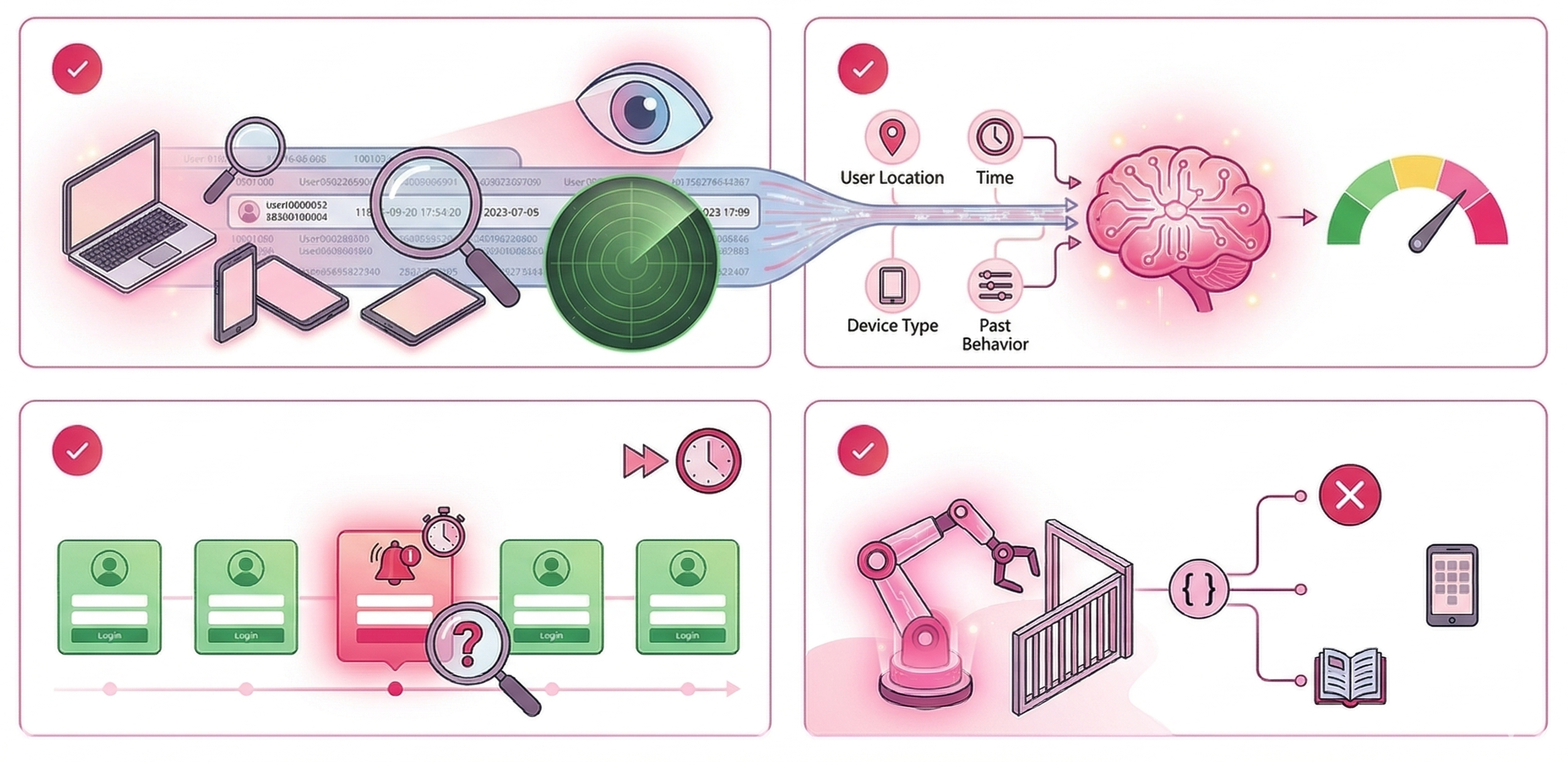
How AI-driven login monitoring Works
Rainbow Secure’s AI-Driven Login Monitoring evaluates every authentication attempt using behavioral and contextual risk intelligence.

-
It continuously analyzes signals including
- Device fingerprint changes
- Location inconsistencies
- Failed attempt clusters
- Privileged login behavior
- IP reputation shifts
- Rapid login velocity
- Abnormal access timing
Each login event contributes to a dynamic risk score
-
When abnormal activity is detected
- Alerts are generated
- Accounts can be temporarily locked
- Sessions may be restricted
- Step-up authentication can be enforced
Login monitoring becomes proactive — not reactive.
Risk becomes measurable — not assumed.

Core Functional Components
Continuous Login Stream Analysis
All authentication events are analyzed in real time.
No delayed batch reviews.
No end-of-day analysis.
No blind windows.




Behavioral Pattern Recognition
The system continuously learns:
• Normal login cadence
• Device consistency
• Typical access times
• Expected geographic regions
When deviation occurs, risk elevation follows immediately.




Dynamic Risk Scoring
Each login receives a calculated risk score based on:
• Context
• Behavioral variance
• Device trust posture
• Role sensitivity
Higher risk → stronger enforcement.
Authentication strength adapts to risk conditions.



Automated Response Triggers
When predefined thresholds are exceeded:
• Step-up MFA is automatically enforced
• Privileges are temporarily reduced
• Sessions are terminated
• Accounts are locked as required
Response is automatic and policy-driven — not manual.




Centralized Risk Dashboard
Administrators gain full visibility into identity risk posture.
Dashboard insights include:
• Login activity heatmaps
• Real-time risk alerts
• Failed login spikes
• Suspicious device attempts
• High-risk user sessions
Identity risk becomes measurable and actionable




- Continuous Login Stream Analysis
- Behavioral Pattern Recognition
- Dynamic Risk Scoring
- Automated Response Triggers
- Centralized Risk Dashboard
Three steps: evaluate risk, decide trust, enforce the right challenge.
Rainbow Secure Adaptive MFA reduces friction when things look normal — and steps up security the moment risk changes.
Evaluate context in real time
Analyze device trust, geo-location, time, login velocity, and behavior signals at login — and again during the session.
Assign risk automatically
Low risk = seamless. Medium risk = step-up. High risk = block + alert. Policies are configurable by role, app, and group.
Enforce the right challenge
Trigger interactive verification, OTP methods, or conditional controls only when needed — attackers can’t replay what they can’t replicate.
Key Security Features
-
24/7 Real-Time Login Monitoring
Authentication activity is monitored continuously — not limited to business hours.
Attackers operate at all times.
Your security does too. -
AI-Based Anomaly Detection
Automatically detect:
• Impossible travel patterns
• Abnormal login velocity
• Suspicious access timing
• Bot-driven credential activityIntelligence detects what static rules cannot.
-
Privileged Login Risk Prioritization
Privileged accounts receive elevated monitoring sensitivity.
Administrative sessions are evaluated with stricter thresholds than standard user access.
High-value accounts demand higher scrutiny.
-
Automated Risk Escalation
When abnormal behavior is identified:
• Risk score increases
• Adaptive MFA is triggered
• Sessions are reviewed or terminatedSecurity enforcement adapts dynamically to risk.
-
Compliance-Ready Reporting
Generate detailed reports for:
• Audit reviews
• Regulatory compliance validation
• Security incident investigationsAll authentication events are searchable, exportable, and audit-ready.


Benefits

-
Detect Compromised Accounts Early
Identify behavioral anomalies before attackers escalate control.
-
Reduce Account Takeover Risk
Adaptive enforcement disrupts suspicious login attempts immediately.
-
Protect High-Privilege Accounts
Elevated roles receive stricter monitoring and rapid enforcement.
-
Strengthen Zero-Trust Enforcement
Trust is continuously evaluated — never permanently granted.
-
Improve Security Visibility
Gain real-time insight into authentication behavior across your organization.

frequently asked questions
-
Is this a SIEM replacement?
No. It complements SIEM platforms by focusing specifically on identity-centric behavioral risk analytics.
-
Does monitoring slow authentication?
No. Risk evaluation is optimized for low-latency enforcement.
-
Can high-risk logins trigger stronger MFA automatically?
Yes. Adaptive authentication policies enforce additional verification based on risk score.
-
Is login activity recorded for audits?
Yes. All authentication events are logged and exportable.


Pricing And Editions
24/7 Risk Analytics & AI-Driven Login Monitoring
Available as
• Advanced Identity Monitoring module. • Continuous Trust enhancement. • Enterprise Risk Analytics package.
Pricing depends on
• 24/7 Threat Response & Protection module • As part of Rainbow Secure IAM Packages
ready to get started?
Every login matters. With Rainbow Secure:
- Login activity is monitored
- Anomalies are detected early
- Risk is evaluated intelligently
- Responses are automated
What Fintech Leaders Actually Need
Assume credentials will be compromised
Do not rely on user awareness alone
Do not break during peak transaction spikes
Reduce fraud losses and investigation fatigue
Cognitive Identity Defense shifts identity from theatrical controls to real protection — without slowing innovation.
Ready To Get Started ? We're Here To Help
Start your journey with us today. It’s quick, easy, and we’re here to help you every step of the way.
Let’s Talk





















